Our publications
BSP’s lawyers regularly share their knowledge through regular legal updates, newsletters and professional publications.
Latest Newsletters & Newsflashes
Apr 19, 2024Vidéo Uplawder | Les spécificités de l'arbitrage au Luxembourg
Notre Partner Fabio Trevisan a présenté l’arbitrage au cours d’une interview vidéo Uplawder . Plus précisément, il évoque dans cet entretien (i) ce qu'est l'arbitrage ; (ii) les spécificités de l'arbitrage à Luxembourg ; (iii) ses avantages ; (iv) les bonnes pratiques ; ainsi que (v) ses retours d
Apr 19, 2024Luxembourg Law of 7 August 2023 on business continuation and modernisation of Bankruptcy Law | Recent case law developments
Following the entry into force of the Luxembourg law of 7 August 2023 on business continuation and modernisation of bankruptcy law (the “ Law”) on 1 November 2023, the Luxembourg courts have handed down several decisions clarifying the scope of application of judicial reorganisation proceedings, the
Apr 17, 2024Listing Act | Multiple vote share structures: provisional agreement reached by Council and Parliament
On 14 February 2024, the Council and the European Parliament have reached a preliminary agreement on the directive on multiple-vote share structures in companies that seek the admission to trading of their shares on an SME growth market (the “ Proposed Directive”). The Proposed Directive is part of
Apr 16, 2024Previously published in Tax
Newsflash | Pillar Two - The Luxembourg Tax Authorities issue a first FAQ Newsflash | Tax measures in favour of the Luxembourg real estate sector
Apr 16, 2024Release of Pillar One Amount B report
On 19 February 2024, the OECD/G20 Inclusive Framework (“ IF”) on BEPS released its report on Amount B of Pillar One intended to simplify transfer pricing aspects of baseline marketing and distribution activities, alleviate administrative burden, cut compliance costs, and enhance tax certainty
Apr 16, 2024ECON opinion on EC proposal for Transfer Pricing Directive
Urgent need to implement harmonized transfer pricing framework for the EU according to ECON On 22 February 2024, the Economic Monetary Affairs Committee (“ ECON”) of the European Parliament adopted its opinion on the European Commission’s (“ EC”) proposal for a Directive on transfer pricing (“ TP
Latest Brochures
Feb 12, 2024ELTIF in a nutshell
The ELTIF was created by Regulation (EU) 2015/760 on European Long-term Investment Funds of 19 May 2015 (and effective from 9 December 2015) (the “ ELTIF 1 Regulation”). The European Long-Term Investment Fund (“ ELTIF”) is a type of collective investment framework allowing investors to invest money
Jun 01, 2023BSP General Brochure
In this brochure you will find the description of all the activity that we can put in place for you. BSP is an independent full-service law firm based in Luxembourg, committed to providing the very best legal services to our domestic and international clients in all aspects of Luxembourg business
Mar 31, 2023Dispute Resolution Brochure
BSP’s dispute resolution practice assists domestic and international clients in a wide range of complex and high-stake and/or international disputes (litigation and/ or arbitration proceedings) in all major substantive areas of the law. Our dispute resolution team can be involved at every stage of
Jul 28, 2022RAIF | Reserved Alternative Investment Funds
This leaflet presents a focus on the Reserved Alternative Investment Fund (RAIF), a new and flexible alternative investment vehicle approved by the Law of 23 July 2016, which entered into force on 31 August 2016 (the RAIF Law). The RAIF Law creates a new type of unregulated fund which has many of
Jul 27, 2022Banking & Finance Brochure
BSP’s banking and finance team assists local and international market players on all regulatory and transactional aspects of Luxembourg banking and financial matters. Our lawyers are reputed for their extensive experience in bank lending, debt capital markets and structured finance, in particular
Jul 27, 2022Tax Brochure
Our Tax practice brochure gives an overview of the services our team of lawyers provides to domestic and internatonal clients in all Luxembourg tax related matters.
Latest Articles & Books
Mar 12, 2024Lexology | Litigation Funding 2024
Our experts have contributed to the publication of a Q&A paper about Litigation Funding in Luxembourg together with Nivalion AG. Look at the chapters below, which are fully investigated in the pdf. REGULATION Overview Restrictions on funding fees Specific rules for litigation funding Legal advice
Feb 12, 2024Chambers | Investment Funds 2024 Guide
The Investment Funds 2024 guide covers 20 jurisdictions. The guide provides the latest information on alternative investment funds and retail funds, including fund formation, restrictions on investors, the regulatory environment, operational requirements and the tax regime. Law and Practice 1
Jan 16, 2024Thomson Reuters Practical Law | Regulation of state and supplementary pension schemes in Luxembourg
A Q&A guide to pensions law in Luxembourg. The Q&A gives a high-level overview of the regulation of national government pensions and supplementary pensions. On national government pensions, it covers employer/employee contributions; national government pension age and monthly amount; and the public
Jan 04, 2024Chambers | Litigation Global Practice 2024 Guide
The 2024 Litigation Global Practice Guide features 70 jurisdictions. It provides the latest legal information on litigation funding, initiating a lawsuit, pre-trial proceedings, discovery, injunctive relief, trials and hearings, settlement, damages and judgment, appeals, costs, and alternative
Nov 20, 2023ThoughtLeaders4 Disputes Magazine | Enforcement of International Arbitral awards in Luxembourg
The Grand Duchy of Luxembourg has a favourable setting for arbitration generally, as well as for the enforcement of arbitral awards. The existence of the award, and the fact that it has obtained the exequatur are sufficient elements for obtaining interim remedies, while the latter is not necessary
Oct 27, 2023Entreprises magazine | Denouncing discrimination and bullying in the workplace
The issue of discrimination and moral harassment in the workplace has become even more topical since the recent adoption last April of the law on the protection of whistle-blowers. For more on this topic, read the article (in French) written by our Partner Anne Morel and Senior Associate Pauline
Latest Videos
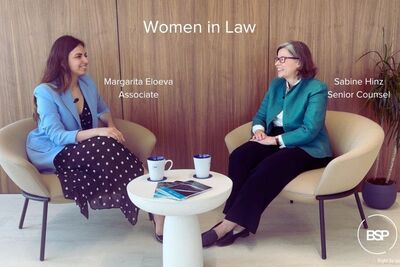
Oct 04, 2023Women in Law Series: Sabine Hinz
Sep 27, 2023Women in Law Series: Evelyn Maher
Sep 21, 2023Women in Law Series: Nuala Doyle
Sep 21, 2023Towards the modernisation of the Luxembourg fund industry
Sep 13, 2023Women in Law Series: Isabel Høg-Jensen
Sep 12, 2023BSP German Desk